Solutions for
- Industries
- Commercial Companies

Cyber attacks exploit weaknesses in systems, applications, and networks. If attackers discover these vulnerabilities before you do, the consequences can include data breaches, operational disruption, financial loss, and reputational damage.
Our penetration testing services simulate real-world cyber attacks to identify security weaknesses, validate defenses, and help organizations strengthen their security posture before threats occur.
We provide controlled, authorized testing performed by experienced security professionals to uncover vulnerabilities and provide actionable remediation guidance.
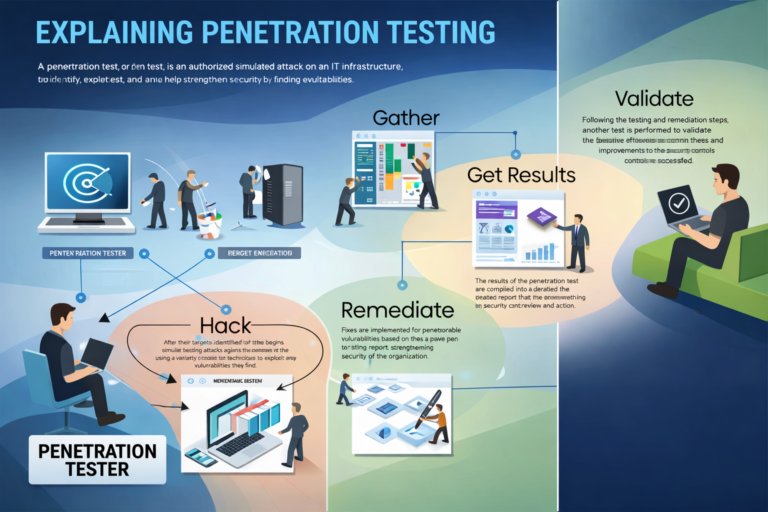
A penetration test (pen test) is an authorized simulated cyber attack performed to evaluate the security of systems, networks, applications, and infrastructure.
The objective is to:
Unlike malicious attacks, penetration testing is conducted ethically and under controlled conditions to help organizations improve security resilience.
Penetration testing provides a realistic assessment of how attackers could compromise your systems and what impact a breach may cause.
Organizations perform penetration testing to:
This proactive approach allows organizations to address weaknesses before they are exploited.
Our penetration testing services evaluate your entire technology environment.
Network Penetration Testing
Web Application & API Testing
We follow industry-recognized testing methodologies such as those promoted by the OWASP Foundation.
Infrastructure & System Testing
Wireless & Access Point Testing
Human & Process Security Testing
We follow a structured and risk-based testing approach to ensure accurate and meaningful results.
We provide flexible testing models based on your security needs.
Testing scope and engagement level are defined based on business objectives and risk priorities.
Security Audit vs Vulnerability Assessment vs Penetration Testing
Organizations evaluate security using multiple approaches:
Penetration testing provides the most realistic view of how an attacker could compromise your environment.
Penetration Testing Deliverables
Our penetration testing engagements provide comprehensive outputs:
These insights enable organizations to make informed security decisions and strengthen defenses.
Organizations using penetration testing services gain:
We combine technical expertise, proven methodologies, and risk-based analysis to deliver accurate and actionable results.
Our approach includes:
We help organizations identify vulnerabilities, strengthen defenses, and protect critical business assets.
Cyber threats continuously evolve. Proactive security testing is essential to protect your organization’s systems, data, and operations.
Our penetration testing services provide the visibility and assurance needed to secure your environment and reduce risk.
Contact us today to schedule a penetration test and strengthen your security posture.